Your SMB in the Crosshairs: What the Glasswing Announcement Actually Changes
A new AI model has industrialized the discovery and exploitation of critical software vulnerabilities. Here’s what it means for your organization — and what you can do right now.

On April 7, 2026, Anthropic — the company behind the Claude AI assistant — announced that its new Claude Mythos Preview model had discovered thousands of critical vulnerabilities in the world’s most widely used software: Windows, macOS, Linux, Chrome, Firefox, and dozens more. Some had been dormant for 27 years. Others had survived millions of automated tests. Mythos found them largely autonomously, for a few dozen dollars each.
If you run an SMB, this article explains why this announcement directly concerns you — and what you can do without a dedicated security team.
Part 1 — What just changed, and why It matters to you
Quebec SMBs: preferred targets for a long time already
Let’s start by correcting a misconception: SMBs are not secondary targets. It’s quite the opposite — and the Canadian data confirms this clearly.
According to a KPMG Canada survey of 735 SMB leaders in 2024, 72% reported having experienced cyberattacks in the past year, up from 63% the year before. More than two-thirds had paid a ransom in the last three years. In Quebec as elsewhere in Canada, SMBs account for more than 60% of cyberattack victims — precisely because they are less well protected. Attackers don’t look for the most lucrative targets — they look for the most accessible ones.
The Canadian data speaks for itself: 78% of businesses have suffered a successful cyberattack; 59% have been hit by ransomware; and when a ransom is paid, only 60% of data is recovered on average — for an average ransom of $160,652 CAD. Recovery costs in Canada doubled between 2021 and 2023, rising from $600 million to $1.2 billion. And 66% of Canadian SMBs still have no plan to deal with a ransomware attack. (Sources: CCCS / KPMG Canada / MicroAge Quebec, 2023–2024.)
What Mythos Preview changes in this equation
If SMBs are already frequent targets, why does the Glasswing announcement change anything?
Because it fundamentally changes the nature of the attacks that all organizations — including SMBs — are now exposed to. Until now, the vast majority of attacks relied on simple techniques: in Canada, 95% of incidents stem from phishing, opportunistic attacks that bet on volume rather than technical precision.
What models like Mythos Preview make possible is the industrialization of vulnerability discovery across the entire application ecosystem — the software that all organizations, large or small, use. Even more significant: the model doesn’t just find isolated flaws. It can chain together multiple vulnerabilities that, taken individually, seem relatively benign, to build a complete and sophisticated exploitation strategy. All of this autonomously, for a few dozen dollars, and without the attacker needing any particular technical expertise.
Before this type of model, developing such an attack required weeks of work by a qualified expert. This cost formed an implicit barrier that filtered targets: an SMB with 20 employees simply wasn’t worth that investment. That barrier is disappearing. The Canadian Centre for Cyber Security (CCCS) confirms that the number of ransomware incidents in Canada is increasing and will continue to increase every year — and the arrival of models like Mythos will only accelerate this trend.
By the Numbers
Before Mythos: Claude Opus 4.6 successfully exploited a Firefox vulnerability 2 times out of several hundred attempts. With Mythos Preview: 181 working exploits on the same test suite. This is not a gradual improvement. It is a change in kind.
Why Quebec SMBs remain particularly exposed
The vulnerability of Quebec SMBs in this new context stems essentially from a structural constraint: limited resources to devote to cybersecurity. This constraint manifests most acutely in the diligence required to keep software up to date — and that is precisely where their greatest exposure lies. A poorly maintained application environment, with updates delayed due to lack of time or dedicated staff, is a standing invitation for attackers who, with tools like Mythos, can now scan and exploit these vulnerabilities industrially. Indeed, 70% of Canadian SMBs report not having the qualified personnel to manage their cybersecurity, and 69% say they lack the necessary financial resources. (Source: KPMG Canada, 2024.)
Added to this is supply chain risk. The CCCS has confirmed that cybercriminals will very likely continue to target managed service providers to maximize the reach of their operations. In 2021, a single attack on one IT service provider compromised 60 service providers and 1,500 of their clients in one operation. If you work with clients or partners larger than yourself, your unpatched systems can become their point of vulnerability.
Finally, there is the gap between perception and reality: 75% of Canadian SMBs fear that generative AI makes them more vulnerable, but 71% still treat cybersecurity as an insufficiently integrated routine. Only 47% say they are ready to face a cyberattack, even though 73% have already reported at least one incident. (Source: KPMG Canada / MSP Corp, 2024–2025.)
Part 2 — What will happen in the coming months
A double acceleration to anticipate
The most concrete consequence for your organization: a double acceleration, on both sides at once.
On the software publisher side, expect to receive more security patches, more often, with greater urgency. Publishers will use these same models to massively scan their own code and discover vulnerabilities they would never have found otherwise. They will have to fix them. Predictable update cycles — Patch Tuesday, monthly updates — will be replaced by more frequent emergency patches. The updates you delay “because the timing is bad” will increasingly become critical fixes that would be dangerous to ignore.
On the attacker side, the window between a patch being released and its active exploitation is shrinking drastically. Today, that delay is measured in days or weeks. With Mythos-level tools, it could be measured in hours. Delaying an update by two weeks was an acceptable risk three years ago. That is no longer the case. The CCCS and its National Cyber Threat Assessment 2025–2026 confirm that Canada is increasingly exposed to actors who combine state-level capabilities with opportunistic cybercrime — and that this trend will accelerate.
Part 3 — What you can do concretely
The good news: you don’t need an exceptional budget or a dedicated team to significantly reduce your exposure. The most effective measures are also the most accessible. They require discipline and organization, not extraordinary resources. And according to the CCCS itself, the vast majority of cyber incidents can be prevented by applying basic measures.
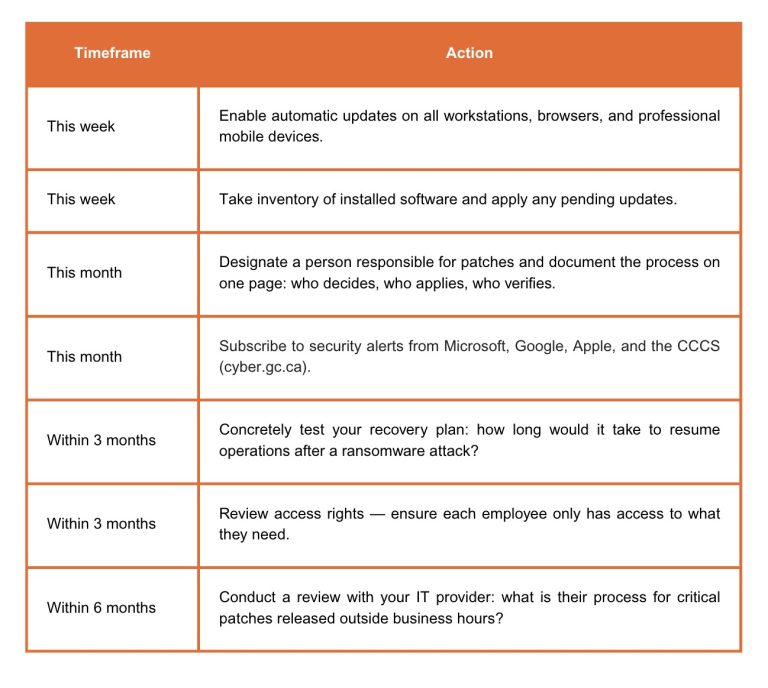
Two important caveats. First, don’t panic and change everything at once: rushed decisions often create more vulnerabilities than they resolve. Second, don’t delegate entirely to your IT provider without oversight: they cannot decide for you whether a service interruption is acceptable in order to apply an urgent patch. Cybersecurity requires an organizational decision, not just technical expertise.
Conclusion
The period ahead will be more difficult for cybersecurity overall, and SMBs are structurally disadvantaged. But organizations that develop the right reflexes now — applying updates quickly, maintaining basic hygiene, testing their recovery plan — will be in a structurally better position in 18 months, regardless of the size of their security budget.
The most likely threat to your SMB remains opportunistic ransomware exploiting an unpatched system, or phishing that compromises an account without two-factor authentication. These threats existed before Glasswing. What’s changing is that the window to address them is narrowing.
Four terms to know
Phishing: a technique that tricks an employee into giving up their credentials or clicking a malicious link. The leading attack vector in Canada, involved in 95% of incidents.
Ransomware: malicious software that encrypts an organization’s files and demands a ransom. The most frequent threat for Canadian SMBs: average ransom of $160,652 CAD, and only 60% of data recovered even after payment.
Zero-day / N-day: a zero-day is a flaw unknown to developers (no patch exists yet). An N-day is a known and patched flaw, but not yet applied everywhere. The majority of successful attacks exploit N-days — hence the critical importance of rapid updates.
Attack surface: the totality of potential entry points into your systems. Every unpatched software, every unused account, every unnecessarily open service expands this surface. Reducing it is the most effective and least costly defense.
Sources
- Anthropic, Project Glasswing — anthropic.com/glasswing (April 7, 2026)
- Anthropic, Frontier Red Team Blog — red.anthropic.com/2026/mythos-preview (April 7, 2026)
- KPMG Canada, Canadian SMB survey, 735 respondents — October 2024
- Canadian Centre for Cyber Security, National Cyber Threat Assessment 2025–2026 — cyber.gc.ca
- Canadian Centre for Cyber Security, Ransomware Threat Overview 2025–2027 — January 2026
- Statistics Canada, Canadian Survey of Cyber Security and Cybercrime 2023 — October 2024
- MicroAge Quebec, National Cyber Threats 2023–2024 — microage.ca/quebec
- MSP Corp, Preparing for the Next Wave of Cyberattacks in Canada: 2026 and Beyond
Inscrivez-vous à l’infolettre Eficio et soyez le premier à recevoir notre actualité !
